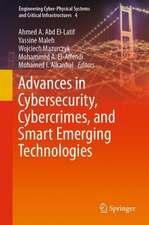
Foundations and Practice of Security: Lecture Notes in Computer Science, cartea 14551
Editat de Mohamed Mosbah, Florence Sèdes, Nadia Tawbi, Toufik Ahmed, Nora Boulahia-Cuppens, Joaquin Garcia-Alfaroen Limba Engleză Paperback – 25 apr 2024
The 27 regular and 8 short papers presented in this book were carefully reviewed and selected from 80 submissions. The papers have been organized in the following topical sections:
Part I: AI and cybersecurity, security analysis, phishing and social network, vulnerabilities and exploits, network and system threat, malware analysis.
Part II : security design, short papers.
| Toate formatele și edițiile | Preț | Express |
|---|---|---|
| Paperback (2) | 340.80 lei 6-8 săpt. | |
| Springer – 25 apr 2024 | 340.80 lei 6-8 săpt. | |
| Springer – 25 apr 2024 | 523.39 lei 6-8 săpt. |
Din seria Lecture Notes in Computer Science
- 20%
 Preț: 558.53 lei
Preț: 558.53 lei - 20%
 Preț: 571.88 lei
Preț: 571.88 lei - 20%
 Preț: 675.83 lei
Preț: 675.83 lei - 20%
 Preț: 1020.28 lei
Preț: 1020.28 lei - 20%
 Preț: 620.33 lei
Preț: 620.33 lei - 20%
 Preț: 560.93 lei
Preț: 560.93 lei - 20%
 Preț: 633.70 lei
Preț: 633.70 lei - 20%
 Preț: 678.21 lei
Preț: 678.21 lei - 20%
 Preț: 1359.66 lei
Preț: 1359.66 lei - 20%
 Preț: 560.93 lei
Preț: 560.93 lei - 20%
 Preț: 733.68 lei
Preț: 733.68 lei - 20%
 Preț: 793.92 lei
Preț: 793.92 lei - 15%
 Preț: 558.12 lei
Preț: 558.12 lei - 20%
 Preț: 793.92 lei
Preț: 793.92 lei - 20%
 Preț: 560.93 lei
Preț: 560.93 lei - 20%
 Preț: 748.63 lei
Preț: 748.63 lei - 20%
 Preț: 562.49 lei
Preț: 562.49 lei - 20%
 Preț: 1246.46 lei
Preț: 1246.46 lei - 20%
 Preț: 449.81 lei
Preț: 449.81 lei - 20%
 Preț: 556.96 lei
Preț: 556.96 lei - 20%
 Preț: 562.49 lei
Preț: 562.49 lei - 20%
 Preț: 851.78 lei
Preț: 851.78 lei - 20%
 Preț: 313.10 lei
Preț: 313.10 lei - 18%
 Preț: 945.44 lei
Preț: 945.44 lei - 20%
 Preț: 314.86 lei
Preț: 314.86 lei - 20%
 Preț: 560.93 lei
Preț: 560.93 lei - 20%
 Preț: 313.87 lei
Preț: 313.87 lei - 20%
 Preț: 1033.45 lei
Preț: 1033.45 lei - 20%
 Preț: 563.29 lei
Preț: 563.29 lei - 20%
 Preț: 733.68 lei
Preț: 733.68 lei - 20%
 Preț: 1137.10 lei
Preț: 1137.10 lei - 20%
 Preț: 735.28 lei
Preț: 735.28 lei - 20%
 Preț: 1079.23 lei
Preț: 1079.23 lei - 20%
 Preț: 560.11 lei
Preț: 560.11 lei - 20%
 Preț: 791.54 lei
Preț: 791.54 lei - 15%
 Preț: 672.87 lei
Preț: 672.87 lei - 20%
 Preț: 1032.47 lei
Preț: 1032.47 lei - 20%
 Preț: 617.17 lei
Preț: 617.17 lei - 20%
 Preț: 1022.15 lei
Preț: 1022.15 lei - 20%
 Preț: 984.64 lei
Preț: 984.64 lei - 20%
 Preț: 620.33 lei
Preț: 620.33 lei - 20%
 Preț: 979.25 lei
Preț: 979.25 lei - 20%
 Preț: 402.28 lei
Preț: 402.28 lei - 20%
 Preț: 316.28 lei
Preț: 316.28 lei - 20%
 Preț: 636.06 lei
Preț: 636.06 lei - 20%
 Preț: 320.24 lei
Preț: 320.24 lei - 20%
 Preț: 328.94 lei
Preț: 328.94 lei
Preț: 523.39 lei
Preț vechi: 654.23 lei
-20%
Puncte Express: 785
Preț estimativ în valută:
92.55€ • 106.13$ • 79.99£
92.55€ • 106.13$ • 79.99£
Carte tipărită la comandă
Livrare economică 27 aprilie-11 mai
Specificații
ISBN-13: 9783031575365
ISBN-10: 3031575369
Pagini: 480
Ilustrații: XIX, 460 p. 120 illus., 94 illus. in color.
Dimensiuni: 155 x 235 x 26 mm
Greutate: 0.72 kg
Ediția:2024
Editura: Springer
Colecția Lecture Notes in Computer Science
Seria Lecture Notes in Computer Science
Locul publicării:Cham, Switzerland
ISBN-10: 3031575369
Pagini: 480
Ilustrații: XIX, 460 p. 120 illus., 94 illus. in color.
Dimensiuni: 155 x 235 x 26 mm
Greutate: 0.72 kg
Ediția:2024
Editura: Springer
Colecția Lecture Notes in Computer Science
Seria Lecture Notes in Computer Science
Locul publicării:Cham, Switzerland
Cuprins
AI and Cybersecurity.- An Adversarial Robustness Benchmark for Enterprise Network Intrusion Detection.- Securing Smart Vehicles through Federated Learning.- Using Reed-Muller Codes for Classification with Rejection and Recovery.- Unsupervised Clustering of Honeypot Attacks by Deep HTTP Packet Inspection.- Security Analysis.- Practices for Assessing the Security Level of Solidity Smart Contracts.- Effectiveness of Binary-Level CFI Techniques.- A Small World–Privacy Preserving IoT Device-type Fingerprinting with Small Datasets.- URSID: Automatically Refining a Single Attack Scenario into Multiple Cyber.- Phishing and Social Network.- Does the Anchoring Effect Influence Individuals' Anti-Phishing Behavior?.- IntelliTweet: a Multifaceted Feature Approach to Detect Malicious Tweets.- Web Scams Detection System.- Vulnerabilities and Exploits.- VulMAE: Graph Masked Autoencoders for VulnerabilityDetection from Source and Binary Codes.- Analysis of Cryptographic CVEs: Lessons Learned and Perspectives.- A BERT-Based Framework for Automated Extraction of Indicators of Compromise from Security Incident Reports.- Enhancing Code Security Through Open-source Large Language Models: A Comparative Study.- Network and System Threat.- Green-Fuzz: Efficient Fuzzing for Network Protocol Implementations.- Unmasking of Maskware: Detection and Prevention of Next-Generation Mobile Crypto-Ransomware.- Automated Attacker Behaviour Classification Using Threat Intelligence Insights.- UDP state manipulation: description of a Packet Filtering vulnerability in Stateful firewalls.- Malware Analysis.- Following the Obfuscation Trail: Identifying and Exploiting Obfuscation Signatures in Malicious Code.- On Exploiting Symbolic Execution to Improve the Analysis of RAT Samples with angr.- Original Entry Pointdetection based on graph similarity.- Attacking and Securing the Clock Randomization and Duplication Side-Channel Attack Countermeasure.- Security Design.- Hardening Systems Against Data Corruption Attacks at Design Time.- Design of an Efficient Distributed Delivery Service for Group Key Agreement Protocols.- A shared key recovery attack on a masked implementation of CRYSTALS-Kyber's encapsulation algorithm.- Tight Differential Privacy Guarantees for the Shuffle Model with k-Randomized Response.