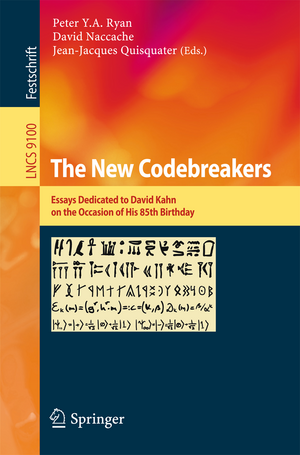
The New Codebreakers
Editat de Peter Y. A. Ryan, David Naccache, Jean-Jacques Quisquateren Limba Engleză Paperback – 18 mar 2016
This book contains 35 talks dealing with cryptography as a whole. They are organized in topical section named: history; technology – past, present, future; efficient cryptographic implementations; treachery and perfidy; information security; cryptanalysis; side-channel attacks; randomness embedded system security; public-key cryptography; and models and protocols.
Preț: 363.35 lei
Preț vechi: 454.18 lei
-20%
Puncte Express: 545
Carte tipărită la comandă
Livrare economică 03-17 iulie
Specificații
ISBN-13: 9783662493007
ISBN-10: 3662493004
Pagini: 568
Ilustrații: XIV, 551 p. 135 illus.
Dimensiuni: 155 x 235 x 31 mm
Greutate: 0.85 kg
Ediția:1st edition 2016
Editura: Springer
Locul publicării:Berlin, Heidelberg, Germany
ISBN-10: 3662493004
Pagini: 568
Ilustrații: XIV, 551 p. 135 illus.
Dimensiuni: 155 x 235 x 31 mm
Greutate: 0.85 kg
Ediția:1st edition 2016
Editura: Springer
Locul publicării:Berlin, Heidelberg, Germany
Cuprins
History.- Mary of Guise’s enciphered letters.- About Professionalisation in the Intelligence Community: the French Cryptologists (ca 1870-ca 1945).- Myths and legends.- The One-Time Pad and the Index of Coincidence.- Technology - Past, Present, Future.- The Fall of a Tiny Star.- Post-Quantum Cryptography: State of the Art.- What is the future of cryptography?.- Efficient Cryptographic Implementations.- Bitsliced High-Performance AES-ECB on GPUs.- Buying AES Design Resistance with Speed and Energy.- Double-Speed Barrett Moduli.- Treachery and Perfidy.- Failure is Also an Option.- How to (Carefully) Breach a Service Contract?.- Information Security.- SpoofKiller: You can teach people how to pay, but not how to pay attention.- Cyber-Physical Systems Security.- Practical Techniques Building on Encryption for Protecting and Managing Data in the Cloud.- Cryptanalysis.- Cryptography as an Attack Technology: Proving the RSA/Factoring Kleptographic Attack.- Dual EC: A Standardized BackDoor.- An Improved Differential Attack on Full GOST.- Cryptographic Hash Functions and Expander Graphs: The End of the Story?.- Side-Channel Attacks.- Polynomial Evaluation and Side Channel Analysis.- Photonic Power Firewalls.- A Heuristic Approach to Assist Side Channel Analysis of the Data Encryption Standard.- Improving the Big Mac attack on Elliptic Curve Cryptography.- Randomness.- Randomness testing: result interpretation and speed.- A fully-digital Chaos-based Random Bit Generator.- Embedded System Security.- Secure Application Execution in Mobile Devices.- Hardware-enforced Protection against Buffer Overflow using Masked Program Counter.- Public-Key Cryptography.- Hierarchical Identities from Group Signatures and Pseudonymous Signatures.- Secure ElGamal-type Cryptosystems Without Message Encoding.- Safe-Errors on SPA Protected implementations with the Atomicity Technique.- Models and Protocols.- Clever Arbiters versus Malicious Adversaries: On the Gap between Known-Input Security and Chosen-Input Security.- Security Analysis of the Modular Enhanced Symmetric Role Authentication (mERA) Protocol.- Crypto Santa.
Caracteristici
Contains lectures given at a Fest in Luxembourg in 2010 on the occasion of David Kahn's 80th birthday The Festschrift includes talks by many of the world's leading cryptographers and security experts Covers a wide range from theoretical cryptography to security applications and from the history of intelligence to recreational applications Includes supplementary material: sn.pub/extras